One Character Off
first → last. Every cooldown, every attribution — silently wrong.
Hey, it’s Arsen
In today’s menu:
• The one-character Solana bug — and what it silently broke
• The security layer Solana just built that other chains wish they had
• Anchor’s ground-up rewrite — 94% smaller, compile-time safe
• And more…
🏴☠️ Vulnerability
Incorrect use of .first() instead of .last() in get_signatures_for_address
From a recent Solana audit — resolved
You audit a helper function.
get_signatures_for_address. Fetches the earliest signature for an address.
Used to track: when was this account first active.
Simple function. One call. One return.
Types line up. Compiles clean.
You move on.
Here’s the question you didn’t ask:
Which direction does the RPC return signatures?
Solana RPC returns signatures newest-first.
The code calls .first().
That’s the most recent signature.
Not the earliest.
Intent and result diverged silently.
let sig = signatures.first();
// Right — list is newest-first, so last() is the earliest
let sig = signatures.last();One character. first → last.
Every check built on “when was this address first active?” got wrong data.
Cooldowns. First-seen gating. Historical attribution.
All silently off.
The kind of bug static analysis won’t catch.
Types match. Semantics don’t.
Only one thing catches this —
reading the RPC contract and asking which direction the list comes back.
🗞️ News
Solana Foundation launches STRIDE + SIRN
Solana Foundation + Asymmetric Research — April 6
Solana just built the security layer other ecosystems wish they had.
Two programs.
STRIDE — a framework across 8 security pillars.
Asymmetric evaluates protocols. Findings published publicly.
Pass with $10M+ TVL → 24/7 monitoring, foundation-funded.
Pass with $100M+ TVL → formal verification, foundation-funded.
SIRN — Solana Incident Response Network.
Founding members: Asymmetric, OtterSec, Neodyme, Squads, ZeroShadow.
Three things shift for Solana auditors:
The bar for protocols above $100M is now formal verification.
Your audit is the first step, not the last.
STRIDE findings are public.
Quality of audit work becomes legible across the ecosystem.
Standards compound.
Solo auditors don’t compete with this.
They pipeline through it.
Firms inside SIRN will surface private audits from monitored protocols.
Getting aligned with STRIDE standards matters.
The ecosystem stopped asking whether security mattered.
It started pricing it in.
📚 Education
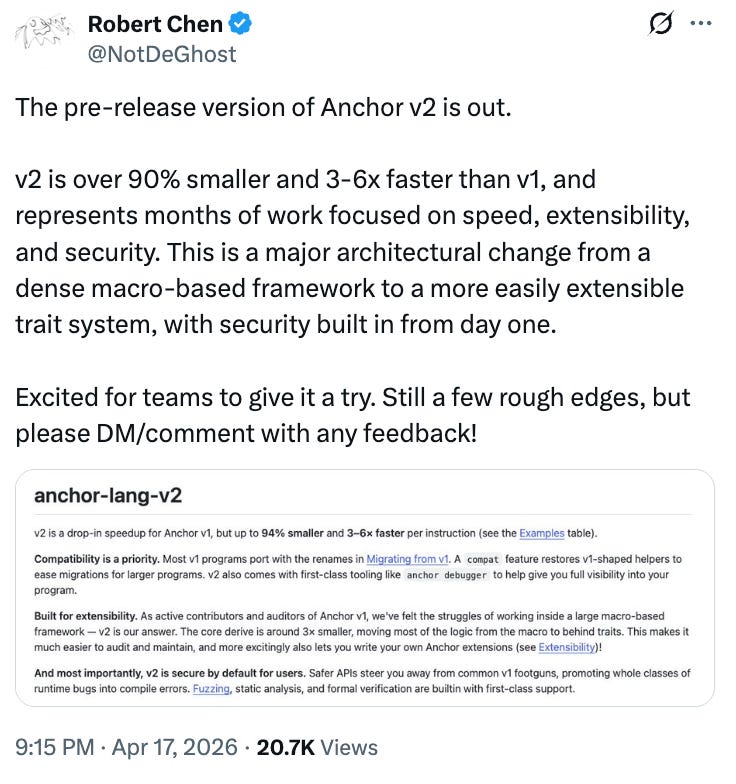
anchor-lang-v2 — the redesigned Anchor framework
Solana Foundation / anchor-next branch
Anchor v1 shaped how auditors read Solana programs.
Five years of macro-heavy derive, runtime checks that didn’t need to exist, a core you couldn’t audit without forking.
v2 is a ground-up rewrite. Alpha, git-only, not on crates.io.
But the direction is right.
The foundation changes first:
pinocchio under the hood,
no more <’info> life times
,#[no_std]` by default. Binaries up to 94% smaller.
CU counts drop 3–6× per instruction.
The account model changes harder. `
Account<T>` is now zero-copy by default — load is a pointer cast, exit is a no-op.
PDA bumps precomputed at macro time for literal seeds.
New Pod wrappers (`PodU64`, `PodVec`…) cast directly from account bytes, no deserialization.
And the safety layer shifts to compile time. Typed `CpiHandle` turns stale-borrow UB into a compile error. Many v1 footguns that used to fail at runtime now refuse to compile at all.
Here’s the part that matters most:
The derive shrinks from ~11,400 LoC to ~3,700.
Which means — for the first time — the Anchor core is auditable.
Fuzzing, static analysis, and formal verification are first-class.
Every v1 audit habit needs updating.
The ones that don’t translate are the ones you most need to re-learn.
That’s it for this week.
Reply with the Solana bug, tool, or pattern you want me to cover next — I read every one.
If a working Solana auditor in your circle would find this useful, forward it their way.
— Arsen, working Solana auditor